Regin, the spy bug revealed by software company Symantec that’s been lauded by security experts for its innovative creation, is likely to have come from the UK and US. Who would have thought?
With reports of its sophistication and technical brilliance flooding the internet, a clearer picture is being painted.
For example, in Symantec’s pie chart which portrayed the infected regions of the world, two notably tech-savvy economic powerhouses were missing, the UK and US.
While China was also absent from this report, it seems unlikely the US would get into bed with what is clearly a cyber-enemy, however, Symantec has not attributed Regin to any state in particular.
Timo Hirvonen, a senior researcher with F-Secure, notes “there are no victims reported from the FVEY countries”, which include the US, UK, New Zealand, Australia and Canada. Interestingly, these all have a joint agreement on ‘signal intelligence’, which includes cyberespionage.
.png)
Confirmed Regin infections by country. Source: Symantec
“Due to its structure, its method of operation, and the professional approach used in programming it, Regin bears the hallmarks of having been created and used by an organised, well-funded operation, probably for the purpose of espionage and surveillance,” Symantec security operations manager Orla Cox told TechNewsWorld.
“While it is likely authored by a government-sponsored group, Symantec does not have any evidence that would link the creation and use of Regin to a particular state or state agency,” she added.
Clearer picture on Regin origins
However, despite Symantec falling short of confirming any US or UK role in the project, an interesting report in The Intercept links the US National Security Agency (NSA) and UK Government Communications Headquarters (GCHQ) – state surveillance operators in both countries – to alleged activities that made use of Regin.
A back door-type Trojan, Regin – as described by Symantec – is a complex piece of malware whose structure displays a degree of technical competence rarely seen.
It’s a multi-staged threat, “and each stage is hidden and encrypted, with the exception of the first stage”.
“Executing the first stage starts a domino chain of decryption and loading of each subsequent stage for a total of five stages. Each individual stage provides little information on the complete package. Only by acquiring all five stages is it possible to analyse and understand the threat.”
Kaspersky Labs has been tracking Regin for a couple of years now, however, its sophistication and stage processes meant it was difficult to pin down.
Now, the company has highlighted the areas targeted by the malware (telecom operators, government institutions, multinational political bodies, financial institutions, and research institutions) and the reasons why it exists (intelligence gathering and facilitating other types of attacks).
Should we be surprised?
Both NSA and GCHQ have hardly been out of the news of late, with whistleblower Edward Snowden’s 2013 revelations followed by smoke, mirrors and double takes, UN lambasting Dragnet practices, GCHQ blaming tech giants on terrorist attacks, pressure on tech companies to comply more, claims that encryption is wrong somehow, reports that another US body spies on its own citizens using airplanes, and now one of the most sophisticated malware attacks in history possibly coming from the same sources.
What’s telling is that, through all this surveillance, very little is being achieved – other than, you know, breaking lots of laws. Ben Wizner, Snowden’s lawyer, recently said the NSA has been sending thousands of referrals to the FBI and not one has led to a lead. He said the FBI pushed back and said it was sending agents on wild goose chases when in fact they would prefer to apply boots and leather to real investigations.
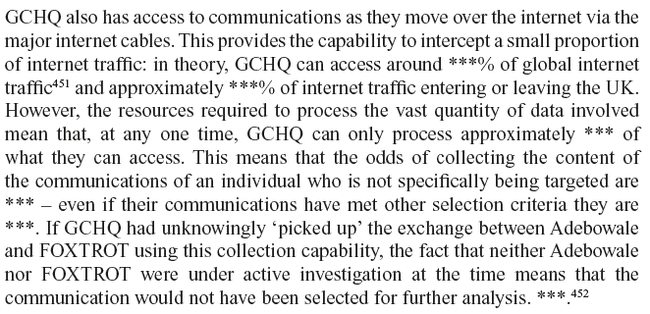
Meanwhile in the UK, the GCHQ’s actual defence for grabbing up anything and everything in the name of ‘state security’ undermines the whole ethos in a ridiculous way. In a report on the intelligence relating to the murder of fusilier Lee Rigby, GCHQ’s limitations on what it can actually process, of all the information it gathers, is revealed – very little.
Extract from the Intelligence and Security Committee of Parliament Report on the intelligence relating to
the murder of fusilier Lee Rigby (UK)
Considering that, from this report, UK Prime Minister David Cameron joined the chorus of those demanding affirmative action from tech giants, essentially telling them to act as guardians of the peace by monitoring our correspondence and telling police what to do and when, is as laughable as it is predictable.
You do wonder, when the postal service was first created, were postmen tasked with monitoring what’s in the envelopes?
Chess pieces representing dark surveillance image via Shutterstock