Malware attacks, especially advanced targeted attacks, have nearly doubled in the first half of 2014, with the UK and Germany being the most-targeted countries, a new report by IT security firm FireEye suggests.
FireEye’s Regional Advanced Threat Report for EMEA, based on data from the FireEye Dynamic Threat Intelligence cloud, reveals the number of unique infections has grown steadily in Europe, the Middle East and Africa (EMEA).
FireEye has examined the activity, attempts and targets of different advanced persistent threats (APT) in the first six months of this year and found government, financial services, telecommunications and energy were the most targeted verticals.
Government, financial services and telecom verticals represented more that 50pc of total APT detections.
“Attackers are targeting high value organisations in (EMEA) and are making their way in,” the report states. “The high number of APT events suggests a large level of information.”
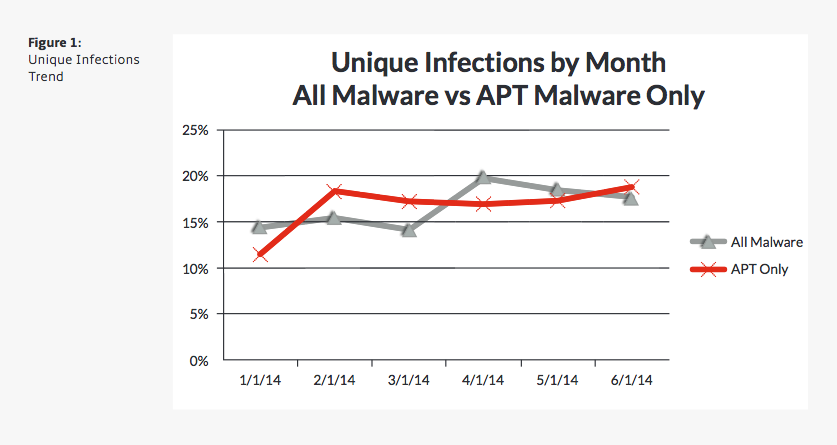
Unique infections trend. Image via FireEye
The UK and Germany were the most targeted countries, at 17pc and 12pc, respectively. They are followed by Saudia Arabia (10pc), Turkey (9pc), Switzerland (8pc), Italy (6pc), Qatar (5pc), France (4pc), Sweden (4pc), and Spain (3pc).
Richard Turner, VP EMEA at FireEye, said advanced attacks are the new reality for business and government.
“By preparing an effective defensive strategy, organisations can avoid the risk of sitting on the sidelines as their data and intellectual property find their way to competitors, adversaries or hacktivists,” Turner said.
IT security tips from FireEye
1. Assume you and your organisation is a target and that your existing security controls can be bypassed
2. Establish a cyber-risk framework that enables the business with board level sponsorship
3. Establish an incident response/management service in a SOC/CIRT team to be able to detect and react to an APT event quickly
4. Enhance your visibility with external threat intelligence to understand who might attack you and how to avoid the tools, techniques and procedures they use
5. Bring in the right technology that could identify an APT
Source: FireEye Regional Advanced Threat Report
Malware image via Shutterstock
FireEye is a Silicon Republic Featured Employer, comprised of top tech companies that are hiring now