Last weekend, Wired reporter Mat Honan suffered a takeover of his digital identity, with hackers gaining control of his Twitter account, shutting down his Gmail, and completely wiping his MacBook. Honan’s experience has highlighted serious flaws in Apple’s and Amazon’s security policies, and both companies appear to be taking steps to prevent a reoccurrence of this incident.
The target of Honan’s attackers was his Twitter account. Not because he is a prominent tech journalist, or even because his account would then give them access to Gizmodo’s Twitter account. No, the hackers simply took a shine to Honan’s three-letter Twitter handle, @mat.
The hackers saw from Honan’s Twitter account a link to his personal website, which gave them his Gmail address. They then entered this address in Google’s account recovery process, which allowed them to see Honan’s alternative email address for this account. Google obscures some characters in these addresses but, knowing their target’s name, it wasn’t hard for the hackers to figure out what m****n@me.com stood for.
Hacking from Amazon to Apple with four digits
This email address comes from MobileMe, an Apple service that has since been replaced by iCloud. Apple’s email accounts are vulnerable and easily accessed, and hackers know this.
The hackers then made a call to Amazon. Pretending to be Honan, they were allowed to change his account information upon giving three pieces of information: an account name, an associated email address, and a billing address. The first two details were already known, and the third came through a simple online search tool.
The hackers were then allowed to add a new credit card number to Honan’s Amazon account, one which could easily have been generated online. They were then able to call Amazon a second time, claiming to have lost access to the account. Using the account name and billing address, plus the new credit card information, the hackers were then able to request a new email address be added to the account. This then gave them access to Honan’s Amazon account details, including all credit cards stored on file. Amazon keeps only the last four digits visible but – what these hackers knew and what we should all be aware of – these are the very digits required to gain access to someone’s AppleID account.
Digital takeover
With this crucial information, the hackers then made a call to Apple’s tech support. Though they could not answer any of the security questions asked of them, Apple’s policy is to then ask customers for a billing address and the last four digits of a credit card number. Verified as far as Apple was concerned, the hackers were then issued with a temporary password to access Honan’s iCloud.
This is the point where Honan’s digital life began to fall apart. By accessing iCloud in his name, they used the Find My Mac service to remotely wipe Honan’s MacBook, erasing all of his files, including all the photos he had of his daughter’s first year. They then deleted Honan’s Gmail account, and eight years’ worth of emails along with it.
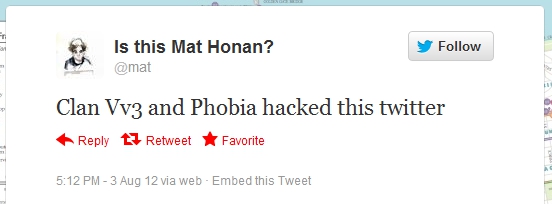
All of this was to prevent Honan regaining control of his Twitter account once it was hijacked. The hackers announced they had taken control, and sent out a slew of racist and homophobic tweets to Honan’s followers. They then posted similar content on the Gizmodo Twitter feed, which has more than 400,000 followers.
Is the cloud secure?
While these attackers didn’t use either the Amazon or AppleID accounts to charge purchases to Honan’s credit cards, or accessed his financial services using the information they had acquired, they could have. The whole incident exposes serious security flaws across various accounts, particularly where policies don’t follow a universal standard.
“The very four digits that Amazon considers unimportant enough to display in the clear on the web are precisely the same ones that Apple considers secure enough to perform identity verification,” writes Honan. “The disconnect exposes flaws in data management policies endemic to the entire technology industry, and points to a looming nightmare as we enter the era of cloud computing and connected devices.”
Moving towards increased cloud usage means these security issues will be more common, and more of a risk, unless addressed now. Though Apple is gearing its customers towards using iCloud, even its co-founder Steve Wozniak is wary of the implications, saying he thinks the shift to the cloud will be “horrendous”.
Honan believes “fundamentally different security measures” are now needed. “Password-based security mechanisms – which can be cracked, reset, and socially engineered – no longer suffice in the era of cloud computing,” he writes.
In the wake of Honan’s ‘epic’ hack, both Apple and Amazon are reviewing their security policies. First, Amazon stopped allowing users to change account settings over the phone and then Apple suspended over-the-phone password resets for AppleID accounts. But these small measures are merely a quick fix and both companies need to work out how to better ensure the security of their customers’ data.